Blogs

LATEST
15 Famous Identity Theft Cases That Rocked The Nation
I have had my identity compromised. It sucks. While I shudder to think about what the thief did with the stolen information, it has forced me to develop good online security practices and get the best identity protection services. Identity theft cases are rising globally, especially in the United States.
The US Federal Trade Commission received nearly 1.4 million identity theft fraud reports in 2021. Apparently, this was fuelled by uncertainty over COVID-19.
Most Common Search Terms That Can Infect Your Kids With Malware

Today’s children are no strangers to computers and the internet. Information and entertainment are just a click away. However, this convenience comes with a catch – the lurking danger of cyber threats.
Children, with their eagerness to explore, often find themselves one click away from potentially harmful content. They are unknowingly drawn into the web of cyberattacks, and it all starts with seemingly innocent search queries.
American Attitude Toward Zoom’s Data Sharing For AI Training

With the rapid growth of AI, worries about cybersecurity and protecting personal data have intensified. The recent signs of companies accessing users’ information for AI training, particularly with the recent update of Zoom’s terms of service, have raised concerns regarding the ethical use of AI.
Most Invasive AI Apps in 2023

Artificial Intelligence (AI) has stirred mixed emotions among tech enthusiasts, professionals, and users. Some believe the technology is the gateway to superior tech advancements, while others view it as a threat because of its ability to intrude on user privacy. But is there any truth to this claim?
By researching the most intrusive AI apps, we have mapped out the power of AI to intrude on your data. This report is a three-section summary of our findings on the invasive nature of AI applications.
Threads Is The Worst Social Media Platform For Protecting User Privacy

In today’s digitally interconnected world, concern over user privacy has become an increasingly pressing issue, particularly when it comes to social media networks. While it is widely acknowledged that most of these platforms struggle to safeguard user privacy adequately, a closer examination of their practices and policies reveals a complex landscape of varying degrees of protection.
How Can I Safely Dispose of My Old Smartphone?

My last office job was managing a help desk for the state government.
I helped with the transition from Blackberry phones to iPhones, but long before that, we were dealing with desktops, laptops, and tablets.
Every year, we’d have a crop of new devices arrive at our door. We’d unbox them and move them into the storage room, where they’d remain as we gradually set up each one and move it to the assigned employee.
As you can probably guess, we also had a lot of old computers ready to be sent off to the computer graveyard.
At first, we just wiped the computer and took it to Surplus Property, the division that handled selling it secondhand to the public.
Over time, though, it became clear that wasn’t enough. Resetting a smartphone or formatting a hard drive doesn’t remove every trace of data. A crafty criminal might be able to grab information from it.
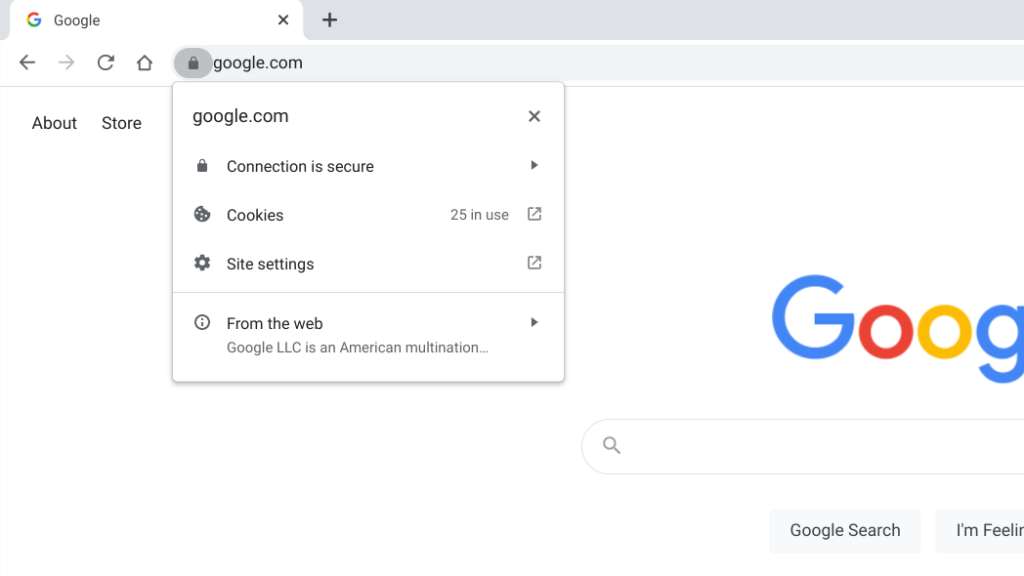
Privacy-Focused Browsers and Search Engines
It’s not that I don’t want privacy. Most of the time, I forget about it.
Yet I always assumed if you wanted complete privacy while browsing and searching, Google’s incognito mode was the way to go.
According to leaked emails from Google employees, though, incognito mode might not be as safe as we think.
Google’s pretty transparent that devices connected to a server can’t use incognito mode to guarantee privacy. In other words, if you’re surfing inappropriately at work, your company’s I.T. team could be watching.
Those Google insider emails indicate your boss might not be the only one who’s watching, however.
Steam Card Scams – What Are They and How Can You Avoid Them?

Few people know Steam scams better than GameStop employees.
As a top retailer of gaming-oriented gift cards, GameStop has watched as consumers come in, seeking to purchase the cards for one scammy purpose or another.
Yet few are as heartbreaking as the one a store manager saw several years ago.
An older woman entered the store, desperate to buy hundreds of dollars in Steam gift cards. The manager asked why, and the woman had a simple explanation:
Is Plaid Safe To Use? What You Need to Know

I have to confess: Every time I see the Plaid logo, I feel a sense of dread.
It has nothing to do with the service itself and everything to do with my password recall (or total lack of it).
My passwords are on autopilot. In case you didn’t realize it, password-keeper apps like Bitwarden, Dashlane, and 1Password tuck all your passwords into a virtual lockbox. If you need a password, it grabs it for you.
That doesn’t work with Plaid, which means one thing:
I have to remember my password.
Military Romance Scams: Keeping Yourself Safe Away from Service Imposters

Finding love is difficult if you travel a lot. You might not know where to go next, it’s hard to settle down, and you can feel isolated even from your friends and family. And a military life often involves just this. It’s difficult for established families and couples, and burgeoning relationships can be extra rough.
The internet, dating apps, and messaging options have made things easier. Contact can be maintained without the difficulties of waiting for a letter. Pictures can be shared. Video calling is often an option. It’s not perfect, but it’s a vast improvement and makes love possible.
Unfortunately, for every situation and potential vulnerability, a scammer hopes to take advantage of that for personal gain.
Fake Online Stores – What You Need to Know

I’m always hesitant to commit to a new app. It’s a big deal, right? Adding an app to my phone means making room for it on my screen, creating an account, and keeping up with a username and password.
There’s a secondary benefit to saying “no” to new apps. I’m less likely to be scammed that way.
Yes, some scams are disguised as shopping apps that promise to offer great products at even better prices.
That’s exactly what cost one woman close to $30,000.
Timeshare Fraud: How To Protect Yourself

I’ll never forget when my mom and dad got a free weekend stay in San Diego. As a ten-year-old, I was thrilled.
Of course, I didn’t understand that free vacations don’t exist. There’s always a catch. In this case, my parents had agreed to listen to a timeshare sales pitch. Listen to an hour-long proposal in return for a free weekend getaway – why not?
As my mom later described, they were held “captive” for over three hours by overly pushy salespeople who tried to push them into signing documents then and there. When my dad said he’d like some time to review the information presented, the salespeople balked.
Mobile Banking App Security: How Safe Are Your Accounts?

If you’re like most of us, you use a mobile banking app. They have become extremely convenient, allow us to avoid a trip to the bank just to deposit a check, allow us to check accounts (or even investments) on the go, and can offer so much more.
However, given that they are linked to what is effectively our financial life, it is rational to have some concerns about it. A leak of your account information could lead to identity theft or just regular old theft. A major security vulnerability could be catastrophic to the industry and people’s personal lives.
Here’s what you need to know about the current state of mobile banking app security and how you can better protect yourself on these apps.
Identity Theft Recovery: Steps To Take If Your Identity Is Stolen
Identity theft is a major problem worldwide and is only growing in popularity among criminals.
There were more than 1.1 million identity theft cases last year in just the United States. This led to the loss of $43 billion in total.
If you’re reading this, you might be worried that you could be one of these cases, but you don’t have to be; you can mitigate losses and regain your identity.
Utility Bill Scams – What They Are And How To Protect Yourself
You’d think scammers would run out of ideas, but they don’t! While they keep coming up with new ways to con you, one scheme that never gets old is the utility bill scam. Everyone pays for electricity, gas, or water, and these crooks just can’t resist taking advantage of it.
So if the scammer randomly tries the utility company bill scam on people, it’s at least going to be a relevant scam. You might take a second or two to remember whether you paid the power bill when the scam message or phone call appears.
In that moment of doubt on your part, the scammer strikes, ramping up the pressure on you to make a snap decision. The scammer hopes you might panic and make a mistake if things feel rushed.
Is McAfee Identity Theft Protection Worth It?

Identity theft protection services are important for helping consumers guard their identity and personal information. They help you spot fraud faster than you may be able to do on your own.
The majority of these services provide comparable advantages, like keeping a watchful eye on the dark web for any instances of personal information being exposed.
However, not all identity theft protection services are created equal.
Some services provide more features that fit your needs. Others may offer a very favorable price point that fits your budget exactly.
For an identity theft protection service to be worth it for you, it must give you the features you need at a cost that’s comfortable for you.
So, is the McAfee identity theft protection service worth it?
What Is Malspam? How Do You Prevent It?
A senior cybersecurity analyst spotted ransomware as it made its way onto his servers.
The malicious email appeared to be an agreement requested by the recipient. But the message included a ZIP file, and that ZIP file was password protected.
Recipients didn’t even have to track down the password. It was provided in the message itself.
When the recipient executed the file, it was set to download ransomware. The ransomware would encrypt the entirety of the end user’s hard drive.
What Is Shoulder Surfing? How It Happens & How Do You Protect Yourself From It

Have you ever noticed someone looking over your shoulder at the ATM? They are probably shoulder surfing to steal your PIN. It has happened to me a few times. In one such instance, I stopped, then turned back and confronted the man.
I told him that he was crowding my space, and I was uncomfortable. Then, I asked him to step back and let me finish. I made sure he knew I was not making a request. He said he was sorry and backed off.
Shoulder surfing is not some new-fangled scam. This type of scamming has been around since the 1980s. Thieves would spy as users punched in calling card numbers and called from public pay phone booths. The scammer would then steal the calling card data for personal long-distance calls or trade them cheaply in the marketplace.
What Is Credit Monitoring?

Here are Home Security Heroes, one of our most frequent recommendations is to invest in credit monitoring services. They have saved millions of people from identity theft and many more from severe consequences should a breach occur. They are simply a fantastic investment for the average family.
Yet what is a credit monitoring service? How do they work, what is their process, and are there any downsides or weaknesses to know? Is signing up for one all you need to do?
A better understanding of the services you are using or intend to use is always good. It helps you choose the right service and make the most of your time, money, and products.
Therefore, here’s what you need to know about credit monitoring services and how to best choose and use one.
Who’s Who In America Scams — What You Need To Know

I was a high school student the first time I found out I was important.
Okay, I was still a total dweeb with my nose perpetually stuck in a book. But there, in black and white, was my name. I was somebody.
My name was listed in a directory called Who’s Who Among American High School Students. I have no idea how I even ended up in the book. I do remember that we bought a copy (of course, we did!).
Yes, it was a vanity ploy. But they also had us believing that being listed in the book might help us with college acceptance and scholarships.
Really, though, it was all about being seen. This was before the Internet and social media. Literally, nobody knew your name unless they went to school with you or met you somehow.
Who’s Who Among American High School Students is no longer in print –– at least not in its original form. Anyone can start a Who’s Who book, though, so it might only be a matter of time before the high school version returns.
How To Identify A Fake Text Message

Someone wants to buy my house.
The funny thing is, they don’t seem to know they’re texting me, not my husband.
Every couple of weeks, someone reaches out, and the messages all follow a similar pattern.
“Jessica from FSCO” wants to speak to us about our house.
“Jason” wants to talk to us about marketing our house.
“Alex” is on the hunt for places to buy in our town.
Alex is annoyingly persistent, texting us multiple times. I ignore every one of them.
Our house isn’t on the market, and even if it was, I’d use a real estate agent, not some rando who text-bombs me every few weeks.
Spamming me is so not the way to win me over.
Credit Repair Scams – What They Are And How To Avoid Them

Qualifying for new credit can be tough if you have a bad history.
That’s why one Texas consumer jumped at the chance to start over.
When she saw online ads promising a “Credit Privacy Number (CPN),” she signed up. With a CPN, she’d get a new number that she could then use to apply for credit.
The number looked like a Social Security number, so it should work, right?
She paid $1,500 for the number, which she immediately began using instead of her Social Security number. Her credit score began notching upward. She found her score in the 700s.
Then federal agents showed up at her work. The mother of three was facing up to 30 years in prison.
That was definitely not good news.
Credit Score Scams – How To Identify And Avoid Them
Looking for an apartment can be a time-consuming process, especially in this market.
So when one consumer found a good prospect on Craigslist, it was time to pounce. First, though, the supposed landlord wanted a screenshot of the renter’s credit score. All the applicant needed to do was click a link and input a name, address, and Social Security number.
The renter did as instructed and received a showing time. The problem? There was no house number listed, and the landlord wasn’t answering calls or emails.
As it turned out, the renter was one of many consumers who have been duped by a rental scam. The issue is so prevalent it merited a BBB scam alert.
How To Protect Your Bank Account From Identity Theft

It was a typical McDonald’s visit.
A Virginia woman made a quick trip through a McDonald’s drive-thru to buy a Happy Meal for her son.
Once she was home, she noticed that more than $300 had been charged to her account. Someone had bought wigs, hair supplies, and food using her card.
As she was on the line with her bank, the woman realized the card in her hand wasn’t her own. The cashier had swapped the cards.
Police were able to access surveillance video that showed the McDonald’s worker using the swapped card to make purchases. Now, the victim is warning others about the dangers of having a debit card in a worker’s hands, even temporarily.
And unlike a credit card, a debit card hits your bank account directly.
MOVEit Data Breach: Everything You Need To Know

Everything about the MOVEit data breach will make you angry.
It has caused millions of dollars in damage to unsuspecting victims who did nothing at all wrong.
Among the victims are public institutions, nonprofits, and schools thrown into chaos because of this callous cyber attack.
And perhaps worst of all – the attack started because of a flaw in a service that was supposed to make things MORE secure.
That’s right – the defenders dropped the ball (more on that later).
We hear about cyber attacks constantly these days. So much that they tend to blend together. Every once in a while, though, a particular attack rises above the rest to capture our collective attention.
MOVEit is one of those attacks.
A Family Member Opened A Credit Card In My Name: What To Do And How To Save Your Credit
If you’re reading this, you are likely in a difficult situation. A family member has betrayed you, using your credit for personal gain by opening a credit card in your name.
Unfortunately, the situation is all too common. That doesn’t make it any less tough emotionally and practically. And all too often, the perpetrator gets away with it.
Don’t be one of the victims who doesn’t get justice. You don’t want this financial albatross hanging around your neck, and you don’t want the situation to get worse.
Here’s what you need to know and what you need to do.
Fake Kidnapping Scams – What They Are And How To Avoid Them

Imagine this:
You’re going about your day, minding your own business, when suddenly your phone rings. As you pick it up, a rush of anxiety surges through your veins, for it’s the voice of someone dear to you, trembling with panic.
Instantly, your skin prickles and a chilling sense of unease washes over you. But what comes next is beyond comprehension. In a desperate, frantic tone, your loved one’s voice pierces the air, revealing a heart-wrenching truth—they’re caught in the clutches of a ruthless kidnapper. Their desperate plea for ransom money strikes you like a bolt of lightning, causing your fear to skyrocket to unimaginable heights.
Unfortunately, when you are in a state of panic, you may not think clearly about what you hear. You might miss clues that tell you the call is not real. And you may not think about calling your loved one directly to see if they’re okay and to verify the story.
Someone Opened A Facebook Profile With My Identity!

It seems unthinkable—almost like seeing your double walking down the street.
What are we talking about? An increasingly common form of fraud creating big headaches and large financial losses for people across the country.
Scammers are creating fake Facebook profiles to pretend to be other people. Even worse, they’re using profiles with your name and picture attached to scam other people…including your friends and family.
If there’s someone impersonating you on Facebook, you need to be aware of it. And once you’re aware—you need to take immediate action.
The following sections cover everything you should know and do. Don’t skip any detail.
What Can Someone Do With My Social Security Number?

The Social Security number system was created alongside Social Security to track benefits due to Americans at retirement and other times.
It is also used as a major form of identification (which explains why it’s so popular with scammers).
It allows access to so many accounts and opportunities, and no other piece of information is so directly tied to a person in this way.
Someone Opened An Instagram Profile With My Identity – What Can I Do?

Instagram impersonation is easier than you think. Many people on Instagram don’t know the real you, there’s probably a post history just waiting for someone to use, and it’s very easy to create an Instagram account.
While it is easy for the perpetrator, impersonation can devastate the victim, especially if they have a strong online presence. Others around the victim might be affected, trust is shaken, and it can go a long time without detection.
If you’re reading this, it has happened to you, or you’re concerned about the possibility, don’t worry. It can be dealt with, and I’m here to help you figure out your plan.
Is The Replika App Safe?
It’s impossible to escape the artificial intelligence (AI) discussion these days.
ChatGPT has gotten everyone’s attention.
Observing the conversations my friends have with ChatGPT, I find myself wondering whether it has started to serve as a replacement for human friendship.
That idea isn’t as absurd as it sounds – in fact, you can already use AI for companionship. And it’s free.
But AI isn’t perfect, and there are some risks with using that technology. Before you download any AI apps, it’s important to know the risks to keep yourself safe.
Review Of Identity Thief Movie — Is It Close To Reality?

We love comedies at my house.
Unfortunately, they’re harder to come by these days. In fact, according to movie research firm Nash Information Services, the market share for theatrical comedies has dropped from 21.34 percent 20 years ago to only 5.34 percent today.
In 2013, comedies were still at 14.88 percent. That might explain how I missed Identity Thief when it debuted in theaters. There were just so many comedies to choose from back then.
The movie was a hit, but it still holds up today, thanks to frequent airings on cable TV.
It’s even on Amazon Prime, which was how I was able to catch it. Today, I see it from a completely different perspective than I would have back then, knowing what I know now about identity theft.
So how true is it to real life? And what lessons can we take away from the movie?
How Do I Remove My Personal Information From The Internet?

I watch many true crime shows – I just saw one before writing this article.
There are a lot of scary people out there. And those people don’t have to look too hard to track down victims.
Take the case of a Japanese pop star whose stalker tracked her down through a reflection in her eye.
Yes, her eye!
See, all this woman did was post a selfie on social media. Her stalker, who proclaimed himself her biggest fan, spotted a train station in the reflection of her eyes.
Using Google Street View, he matched the train station and located her.
It might seem like an extreme case, but is it really? How often do we post pictures of ourselves online? And as high-definition images become the norm, those little details could put us at risk.
Debt Collector Scams – What They Are And How To Avoid Them

I’ve only been contacted by a debt collector once. It was terrifying.
They didn’t threaten me or anything – I’m just a lightweight and do not like being called out for breaking the rules.
In this case, it was an apartment I’d rented for a year or two a couple of years earlier. I’d moved out and was surprised they returned my security deposit. Apartments tend to find some excuse to keep it, in my experience.
Sure enough, they’d been trying to reach me about “damage” they’d found to the apartment. Never mind that I was hardly ever there, I owned no pets, and I’d made a point to clean it thoroughly.
Their attempts to track me down to collect this debt had been unsuccessful. So they’d turned it over to collections.
What Are Data Brokers And How Can You Keep Your Information Safe?

Years ago, I entered a contest to win an amazing vacation.
Only after I’d dropped my entry into the fishbowl did I stop to think about what I’d just done.
Sure enough, within days, my phone was ringing with a pitch from a pushy salesperson. I hadn’t won the vacation, but I could still go on that trip for the low, low price of…
You get the drill.
This was before social media took over our lives – and before we willingly handed over all our information, including photos of our meals, kids, and new cars.
Nothing is free, though…not even social media. When we share all this information, we’re handing over something more valuable than money:
Our data.
Telegram App Scams: Keeping Fraud Out Of Your Inbox

Frequent users of Telegram will tell you that the app can be all-consuming, overwhelming, and quite helpful for keeping in contact with people. Joining a group on Telegram can let someone meet someone new and get in touch with people with common interests.
It can also be a very good way to keep in touch with friends who refuse to use anything else.
However, like any other social media or messaging app, some do not have the best intentions. Scammers and cybercriminals have their plans for any successful online enterprise.
Over the last few years, we have seen a rise in scams and phishing attempts on Telegram.
I don’t want your experience on the app to be ruined, and you don’t want to deal with identity theft, stolen property, or the other potential consequences of falling for a scam. Therefore, it’s best to learn what you can do and how to protect yourself.
Dave Ramsey Identity Theft Protection: What Is He Selling And Is It Good?
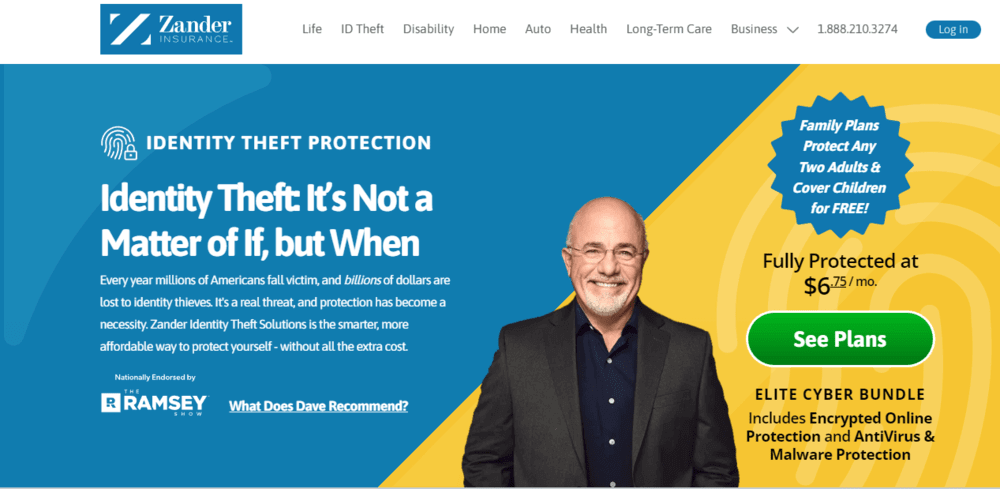
In passing, you’ve probably heard the name Dave Ramsey before, even if you don’t know what he does or advocates for.
The personal finance celebrity has long been working to give people more control and information over their finances. He’s become a household name in talk radio as a result.
As part of this, he advocates for some products and practices. Protecting oneself from identity theft is one of those positions (and one we agree with).
However, to do so, he recommends Zander, a leading identity theft protection service that has partnered strongly with Dave Ramsey.
What Are Hospital Bill Scams And How To Avoid Them

Being served legal papers is no fun.
So when a Mississippi consumer got a phone call asking them for an address, it was no doubt scary at first.
The caller claimed to be trying to serve papers about an unpaid medical bill. The caller even knew the person’s partial address and the last four numbers of the Social Security number.
Still, something didn’t feel right.
The person asked for the name and phone number of the business calling and immediately tried to call back. The company was called Document Delivery Services, based in Nevada.
When the person contacted the business office of the local hospital, it turned out there wasn’t an unpaid bill. It had been a scam attempt.
Luckily, that scam attempt failed.
How Do I Know If My Device Has Malware Or Spyware?

Around 10 percent of all computers get attacked by malware and spyware every year.
Is yours one of them?
The answer, unfortunately, is eventually “yes” for everyone.
The numbers suggest that ALL computers fall prey to malicious software at least once a decade. Some get infected more often than that. And depending on how you use your computer, the odds of encountering malware go WAY up.
Here’s where things get especially troubling: Your computer could have a threat (or many threats) hiding inside, watching what you do, recording your activities, and stealing your data…and you would have no idea there was any problem at all.
Sweepstakes Scams: How To Identify And Avoid Fraudulent Schemes

“YOU Won!!!”
What could be more exciting to hear? And who doesn’t want to be a winner—especially when it comes with a prize?
This could be the best news you ever hear…or a trap that ruins your life.
If you play the lottery, enter contests, or participate in sweepstakes of any kind, you could be a target for scammers.
But here’s the truth: Even if you never test your luck, you might still fall victim to a sweepstakes scam. And the more you think you’re immune, the higher the risk becomes.
You lower your risk of these scams with good information and common sense safety measures. Find both below. By the end of this article, scammers will wish they’d never tried to mess with YOU.
Signal App Scams: Protecting Yourself From Scammers On The Privacy-Focused Messaging App
Scams are part of the Internet. Scams have become part of many messaging services as a result.
Signal, a more privacy-focused app that millions of people use globally, is not an exception, and scammers are regularly working on ways to get people to part from their information and money on the platform.
So what do you need to know, and what do you need to do? I’ll guide you through the scams, the defenses, and how it all works
Apple ID Scams: Don’t Let Scammers Take A Byte Out Of Your Identity

If you’re a MacOS user or know someone that is, then you know how important an Apple ID is. It’s up there with Facebook, Google, and Amazon as an account that links to practically everything.
And Apple is one of those companies that essentially has your life in digital format, isn’t it?
That makes an Apple ID account valuable to hackers, scammers, and others.
And while accessing Apple’s database or controlling such information is the cybercriminals’ Holy Grail, it’s thankfully tough to crack (except for that one time).
Therefore, the lesser cybercriminals of the world send out various Apple ID scams, hoping to get a bite and get people’s information in the process.
If you’re an Apple user, don’t let this be you.
So what do you need to know about Apple ID scams, and what can you do? I’m here to guide you through that question, so keep reading.
Twitter Scams – What They Are And How To Avoid Them

Social media scams can become so predictable.
That’s why one Twitter user decided to have a little fun with her scammer.
When a man contacted the woman claiming to be her one true love, she was amused.
When he asked for $3,200 to visit her, she had a better idea. She’d travel to see him.
And that was when her imaginary journey began. She sent a series of pictures of her “travels,” which included crashing in a helicopter and being stranded in the snow.
Of course, she’d never left home. But her tales panicked the scammer, who begged her to stop traveling and simply send her the $3,200 so he could come to her.
It wasn’t the first time the 42-year-old self-proclaimed bored Twitter user had fun with a scammer. Typically, her conversations end with the scammer blocking her. But at least she’s never lost a dime to a Twitter scam.
8 Dangers Of Posting Your Pictures And Information Online

I’m probably going to offend many people here, but posting your pictures and information online is dangerous.
Wait, I’ll explain.
It’s okay to share beautiful moments like Christmas trees, Thanksgiving, and other festive periods with your friends on Facebook and Instagram.
But many people tend to overshare, revealing sensitive details in pictures that shouldn’t be made public.
How Easy Is It For Someone To Steal Your Identity?

How often have you clicked a link online, especially on social media? You’ve probably lost count.
Me too.
But clicking one URL cost me nearly $6,000 in 2013. It was supposed to be a YouTube link to watch the recap of the Super Bowl XLVII between the 49ers and the Ravens.
The 49ers lost, which hurt, but I had no idea another heartbreak would come from the URL I clicked.
Unfortunately, it was a phishing link that installed spyware on my device. It resulted in hackers accessing my personal and financial information.
How To Tell If Someone Is Using Your Identity

When I got scammed of $5,700 in late June 2013, I only found out after a store refused my personal check.
The damage had been done.
That’s the reality of identity theft. You usually don’t know until it’s too late.
And if I didn’t walk into that store, the financial losses could have been even more disastrous.
Millions of Americans suffer from identity theft yearly. Identity theft happens when someone uses your personal information to steal money or commit crimes.
I lost six thousand dollars, which is a lot of money. But it could be worse for others.
How To Prevent Identity Theft

Identity theft is the fraudulent practice of using someone else’s name and personal information to steal, obtain loans, credit, etc.
It sounds like something straight out of a crime blockbuster movie until it happens to you.
Let me tell you a story about how my life changed a decade ago.
In late June 2013, a store refused my check after running it through a verification service.
Like everyone would, I called my bank immediately. What I heard was shocking.
TWELVE checks had been written on my account, and a total of $5,700 had been withdrawn.
I admit. I am an impulsive spender.
BUT NOT LIKE THAT.
How To Protect Your Identity Online
What if protecting your identity online was easier than you thought?
At first glance, figuring out how to protect your identity online feels like a monumental and complicated task. You know it’s important, but where do you even begin?
That’s where these 12 simple steps come in.
If you put all of these into practice, stealing your identity would be a near impossibility. And you can act on most of these in as little as a few hours.
So, if protecting your identity online is something you’ve been meaning to get around to, there’s no better time than now.
How To Protect Seniors From Getting Scammed

Seniors like our parents and grandparents aren’t tech-savvy, which already makes them vulnerable to being scammed.
Plus, they tend to have more money in the bank because they’re retired or close to and have a fixed income.
Put these variables together, and it’s no wonder they’re the likeliest demographic to be fraud victims after children.
For example, American seniors aged 60 and above lost over $1.6 billion to fraudsters in 2021 alone. And studies show this doesn’t tell the whole story.
How To Protect Your Child’s Identity Online

You need to protect your child’s identity online. If not, they’ll be part of the 1.3 million kids with their identities stolen yearly.
And there are dire consequences.
For example, you don’t want to realize your child’s identity has been stolen and used to commit financial fraud when it’s time for college.
But beyond financial risks, you should protect your child’s identity from creeps. Your child could also be used as a weak link to target the entire family.
Children are innocent. So, they’re more vulnerable to cyber-attacks.
How To Remove Hard Inquiries From Your Credit Report

It starts out innocently enough.
You hear about a great interest rate on a personal loan, or you apply for an apartment that offers a lower monthly rent than what you’re paying now.
But without realizing it, you may have lowered your credit score.
The credit reporting agencies classify two types of credit checks: hard and soft. With a soft inquiry, a creditor simply checks your score to make sure you qualify. These often happen with creditors that advertise they’ll “preapprove” or “preauthorize” you for an opportunity. Soft credit checks don’t show up on your credit report and don’t impact your score.
Zelle Scams – What They Are And How To Avoid Them

I remember the days before peer-to-peer payment services.
Most of the time, credit and debit worked fine. But there were times when you just needed to hand cash to a friend. Sometimes, we’d have someone come to the house to do work, and paper checks were the only option unless we happened to have hundreds of dollars in cash on hand.
We never do!
Now, thanks to apps like Zelle and Venmo, we can zap cash to anyone we need. I use these apps to send money to colleagues collecting flowers for a peer. Sometimes my stepdaughter needs a little extra cash.
How Does Tax Identity Theft Occur?

Last summer, a Pennsylvania college student received a letter in the mail from the IRS. Had she filed a tax return?
The answer was no, but to set the record straight she had to agree to a video call with an IIRS agent. Once that was done, she thought the drama was over, but it had just begun.
On March 15 of this year, the student received another IRS letter. Once again, another tax return had been filed in her name and a refund was on the way to the filer.
The student had to get in touch with the IRS. This time, she had to wait 40 minutes to tell someone that this other return was fraudulent. Finally, the return was flagged and the IRS promised to look into it.
Unfortunately, the issue had an inconvenient side effect – she was a dependent on her parents’ tax return. Due to the repeated fraudulent returns, though, her parents could no longer file electronically. They had to file a paper return.
The Dark Web: What Is It & How Hackers Sell Your Identity On It For Pennies

In 2015, my co-worker Mike told me about the dark web and the insane things that happened there.
I couldn’t quite wrap my mind around how there was a place where people could anonymously sell personal information or even hire hitmen online!
Right there, Mike asked for my wife’s name and, within seconds, found her Social Security Number for sale – for $2.50!
There’s more.
The website he found it on claimed to have over 160 million other SSNs and dates of birth for sale. That was half of the United States population at the time.
Venmo Scams – What They Are & How To Avoid Them

When a Detroit woman saw a post offering Morgan Wallen tickets on social media, she couldn’t resist the deal. The seller said she’d bought them for her daughter’s birthday, but that she couldn’t use them.
The buyer did exactly what we’ve all been advised to do. She clicked over and took a look at the seller’s profile. It looked legitimate.
She sent the money and waited. The seller claimed she was having trouble sending the tickets, then vanished. The tickets never came.
Worse, within days, the buyer’s bank account was emptied by the seller. Apparently, the scammer had hacked her Venmo account, accessed her debit card information, and found their way into her bank account from there.
Yikes!
So, what is this scam? And, how can you avoid it?
PayPal Scams – What They Are & How To Avoid Them

Like many of us, I’ve had a PayPal account for years.
I remember using it for the first time when I began shopping on eBay.
Maybe I’m old-fashioned, but I prefer my PayPal account more than newer digital payment methods like Venmo and Apple Wallet.
I can still recall a few scam emails I got in the early 2000s. Since I worked in information systems at the time, I knew better than to click links. I’d cleaned up more than a few viruses caused by those clicks. I always went straight to PayPal, logged in, and checked to see if there were any issues with my account.
But it’s not as easy to avoid scams these days. PayPal scammers can be pretty creative in getting you to click. It can be hard to tell what’s real and what’s phony.
Luckily, we’re here to help.
How To Recognize And Avoid Multilevel Marketing Scams

I am not a salesperson. It’s at the very bottom of my list of skills, and I know it.
But one night, way back in the 2000s, a friend almost had me convinced.
She was a salesperson for a very well-known multilevel marketing company. I knew for a fact she wasn’t making all that much money doing it, and she was amazing at selling it. She was constantly having cosmetics makeup parties at her house, where she sold a few items at each event.
One Friday night, she asked me to go with her to a recruiting session. We were hanging out anyway, so what was an hour or two? It might be a fun adventure, I figured.
How To Spot And Avoid Gift Card Scams

I make it a habit to check my bank accounts every morning, just in case.
One morning, it paid off. I woke to find someone had charged $4,000 at McDonald’s and Hardees. They showed up on my statement as eight charges of $500 at each location.
How could someone spend $4,000 on fast food, I wondered?
As it turns out, I’d fallen victim to one of the best-known gift card scams. Someone uses a stolen credit card to purchase gift cards. Since gift cards operate as cash, even after I reported the fraud, there was nothing anyone could do. The thieves had a lifetime supply of Big Macs and Made from Scratch Biscuits.
Luckily, our credit cards have fraud protection, so I wasn’t liable, but it was an introduction to why gift card fraud is so popular with scammers.
Snapchat Scams – What They Are And How To Avoid Them

When a California teen received a flirty Snapchat message, he eagerly went along with it.
After all, the flirty user, who went by the name Errina Angels, was offering $500 a week if he agreed to be her “sugar baby.”
But when she wanted him to deposit two checks into his bank account, his Spidey Senses went on alert. However, he did as requested. He deposited the two checks she sent, then forwarded the funds to her via Zelle, minus the promised $500 he could keep for himself. The checks bounced.
Even though the victim of the scam was only 17, his bank wouldn’t cover it. He’d authorized it, after all.
Instagram Scams – What They Are And How To Avoid Them

His heart was in the right place.
When a North Carolina man received a direct message on Instagram, he immediately took action. The friend claimed to be locked out of Instagram and needed his help. All he’d have to do was click on a link to verify he knew the locked-out person.
He clicked on the link then input his name into the page that appeared to be an Instagram login page and was immediately locked out.
It took months for the user to regain access to his account. By then, the scammer had posed as him on Instagram, posting to his feed and directly messaging his friends and family. It only took seconds for the man to fall victim to one of the most popular social media scams:
The imposter scam.
Craigslist Scams: Everything You Need To Know

Want to feel awake and alert? You don’t need a cup of coffee – here are some facts that work just as well.
Every month on average, people create around 80 million posts on Craigslist.
Research shows that 1.5 percent of all the listings posted on the site are scams. Crunching the numbers reveals something truly alarming – there are 1.3 million scams on Craigslist at any given time.
Craigslist is great at connecting buyers and sellers, employers and job seekers, or people and communities. Unfortunately, since the site first started it has also excelled at connecting scammers with victims.
Amazon Scams: Protecting Yourself, Your Porch, And Your Accounts

How many emails or communications from Amazon have you gotten in the last week, in one form or another? Did you get a couple or a few dozen? For some people, Amazon effectively rules their online and shopping lives.
It’s some combination of impressive and scary.
With all the money going into Amazon, it stands to reason that scammers would want a piece of that annually-cooked $500 billion pie. And they realize trying to trick consumers is easier than trying to trick Amazon (most of the time, anyway). Therefore, scammers will try every scam variant they can think of.
Work-At-Home Scams – Learn To Identify Them And Protect Yourself

Even after the world returned to normal from the Covid-19 pandemic, working from home remains a viable option to generate income.
For many people, working from home is a good career move. Greater life-work balance can be achieved more easily when the daily commute is eliminated, along with the long hours at the office.
But the idea of working from home or “work-at-home” was around before the pandemic. And while some of those opportunities were legitimate then, many people were falling for fake opportunities devised by scammers.
This does not mean that you need to outright give up the idea of working remotely. There are still many genuine opportunities you can take advantage of. However, it is of utmost importance that you remain aware of the dangers involved in work-at-home scams.
Home Title Scams – What They Are And How To Avoid Them
Most of us are familiar with credit card fraud and banking fraud. We may even take steps to avoid things like tax fraud scams. However, another type of fraud that you need to understand if you are a property owner is a home title scam.
Home title theft is part of the wide-ranging world of scams that cost American consumers nearly $8.8 billion in losses in 2022, according to the Federal Trade Commission.
Protecting yourself against home title scams requires spending a bit of time guarding your personal data. You also need to be able to recognize the different types of techniques scammers use when your home’s title is in the crosshairs.
We’ll explain everything you need to know about home title scams. Most importantly, we’ll provide some tips to help you avoid them too.
Geek Squad Scams – Protecting Your Identity From Tech Support Impersonators

People trust Geek Squad, right? I should trust Geek Squad, right?
That is the typical thought process of someone who falls for Geek Squad or Tech Support scams. In truth, you can trust Geek Squad itself.
The problem is scammers and scammer groups impersonating Geek Squad for their own ends.
If there is trust in an organization, a scammer will exploit that trust. Therefore, we have Geek Squad scams, which can result in identity theft, stolen accounts, and monetary loss.
However, you can defend yourself from these scammers and arm yourself with the knowledge to prevent this scam from affecting you and your household. HomeSecurityHeroes has everything you need.
Facebook Marketplace Scams: How To Recognize Them And Protect Yourself
Facebook Marketplace first started making waves in 2016. It’s now used by millions of people to sell and buy items of all kinds. People buy products, sell services, and even rent houses through Facebook Marketplace every day..
There are tons of genuine people who use Marketplace. The problem is there are also tons of scammers – and all they want is to steal your hard-earned cash.
In 2021 alone, about 17 percent of the people who used Marketplace were scammed. Every minute of the day, six fake accounts were made. Those are impressive numbers that illustrate the importance of protecting yourself.
At the same time, Facebook Marketplace is huge for legitimate users. One billion people access this online shopping destination every month.
What Information Hides In Your IP Address?

“My what?”
An IP address – that ultra-boring, long number issued by your Internet Service Provider (ISP)?
Yes, that one.
Paying so little attention to it can become a HUGE source of grief since an IP address is a very valuable digital asset that a threat actor could use for malicious purposes. So, what’s the potential harm if your IP falls into the wrong hands?
Let’s dive in…
Text Message Scams – Common Scams And How To Protect Yourself

I get them, and YOU get them.
Those text messages that appear like spam or just seem a little odd.
Perhaps they’re an old contact that doesn’t sound like themselves texting out of nowhere.
Perhaps you won a lottery you know you didn’t sign up for.
Or, it could be borderline gibberish in SMS form.
Most of these texts are scams and part of a family of text message scams that have become more prevalent in recent years.
Not every text you get is there to benefit you. Many messages attempt to scam us out of financial or personal information. In other cases, it’s a more common scam to get us out of our money after developing trust with a stranger.
Here’s what you need to know about text message scams and how to deal with them.
WhatsApp Scams – What They Are, How To Identify And Avoid Them

The days of landline calls and plain text messages are now a distant memory.
With the advent of social media and instant messaging apps, the way the world communicates has inherently transformed in recent years.
At the forefront of the change is WhatsApp, the instant messaging app that is now recognized worldwide.
The popularity of WhatsApp is astounding, with over two billion people and five million businesses across 180 countries using it daily.
With support for over 60 languages and convenient features like voice and video calls, group chats, and file sharing, WhatsApp has become an inexorable part of our daily lives.
Rental Car Scams – What They Are And How To Avoid Them

It always pays to stay awake, alert, and on the lookout for potential scams.
In fact, one of the most important things to remember is that as time passes and situations and realities change, scams also change. Scammers are regularly coming up with new schemes and techniques, a lot of which are dictated by the unique characteristics of situations. The world of rental car scams is a great example.
The rental car industry has always been loosely associated by many with certain unscrupulous or questionable business practices. In recent times, the urge for people to travel after the long isolation of the pandemic has resulted in a dramatic surge in demand for rental cars.
7 Serious Consequences Of Being Victim Of Identity Theft

With the widespread use of the internet, smartphones, and social media, identity theft is a significant problem for consumers. Scammers and criminals continue to develop new ways to steal people’s personal information online, using their confidential details to commit fraud.
The consequences of identity theft are serious and affect people’s lives and health in various ways. In addition to lost time and money, identity theft causes anxiety and sleep problems because of financial and emotional stress. Depending on the type of crime, the damage can last days or years, and even after the issue is resolved, victims live with the fear of it happening again.
Lost Your Wallet? Here’s The 11 Things You Need To Do Right Away

I was at a business conference the last time I lost my wallet.
I’ll never forget the panic that set in. Your first thought is to find it. You look everywhere. Then you start backtracking. Did you leave it at the restaurant? In your hotel room? In your car?
Once the reality starts to set in, though, you do a quick inventory of all that you might have lost. In my case, it was…
6 Must Do Things Immediately After Losing Your Credit Card

The last time I lost my credit card was a decade ago. I can still remember it like it was yesterday.
I pulled out my wallet to pay for a purchase, only to find an empty slot where that gray piece of plastic should be. Of course, my first move was to search my purse, my pockets, my car, and everywhere else that wallet had been.
My second move was to retrace my steps.
Luckily, in that case, I could clearly remember the last time I’d used it. We’d eaten at a pizza place the previous night. I crossed my fingers and called the restaurant. I got very, very lucky. They had the card.
How To “Freeze” Your Social Security Number

The last time I lost my credit card was a decade ago. I can still remember it like it was yesterday.
I pulled out my wallet to pay for a purchase, only to find an empty slot where that gray piece of plastic should be. Of course, my first move was to search my purse, my pockets, my car, and everywhere else that wallet had been.
My second move was to retrace my steps.
Luckily, in that case, I could clearly remember the last time I’d used it. We’d eaten at a pizza place the previous night. I crossed my fingers and called the restaurant. I got very, very lucky. They had the card.
How To Protect Passwords From Hackers and Identity Theft

When I worked in I.T., I always knew where to look for passwords.
I’d be stuck in someone’s office, trying to troubleshoot an issue. At some point, I’d need to log in as the end user, and that was when I’d start searching.
I was surprised at how often that password was hidden under the keyboard. Sometimes they were even posted on the keyboard tray on sticky notes, visible to anyone who entered the office.
In a few cases, the passwords were stuck to the monitor.
We, of course, discouraged all that, but it still came in handy when I really needed the password.
The problem was, it would also come in handy to anyone who entered that office. Our building was secure, but there were cleaning crews in and out of there at night. It wasn’t too out of the question that someone could log in as that user.
That’s when the real damage can be done.
What exactly can a scammer do with a lost or stolen password? Read on to find out.
How Do Hackers Hack Your Phone?

In May of last year, a woman suddenly found that her cell phone no longer worked. She contacted her provider, Spectrum, to have them check into it.
As it turned out, her phone had been hacked.
And, the damage was far-reaching. Soon, the criminals opened credit cards in her name, and stole money from her personal and business accounts.
Although the victim was never 100 percent sure how the hackers accessed her phone, she’d been traveling recently. Authorities believe the incident may have happened while she was using public Wi-Fi.

