AN AI JUST CRACKED YOUR PASSWORD
We used an AI password cracker to run through 15,600,000 common passwords to find out how long it will take AI to crack your password in 2023.

Think you have a strong password against AI? Find out below.
An AI would need about
Instantly
to crack your password
We used an AI password cracker called PassGAN to run through a list of 15,680,000 passwords. Here is what we found:
Time It Takes Using AI to Crack Your Password [2023]
| # OF CHARACTER |
Numbers Only | Lowercase Letters | Lowercase Upper & Letters | Numbers, Upper & Lowercase Letters | Numbers, Upper & Lowercase Letters, Symbols |
|---|---|---|---|---|---|
| 4 | Instantly | Instantly | Instantly | Instantly | Instantly |
| 5 | Instantly | Instantly | Instantly | Instantly | Instantly |
| 6 | Instantly | Instantly | Instantly | Instantly | 4 Seconds |
| 7 | Instantly | Instantly | 22 Seconds | 42 Seconds | 6 Minutes |
| 8 | Instantly | 3 Seconds | 19 Minutes | 48 Minutes | 7 Hours |
| 9 | Instantly | 1 Minutes | 11 Hours | 2 Days | 2 Weeks |
| 10 | Instantly | 1 Hours | 4 Weeks | 6 Months | 5 Years |
| 11 | Instantly | 23 Hours | 4 Years | 38 Years | 356 Years |
| 12 | 25 Seconds | 3 Weeks | 289 Years | 2K Years | 30K Years |
| 13 | 3 Minutes | 11 Months | 16K Years | 91K Years | 2M Years |
| 14 | 36 Minutes | 49 Years | 827K Years | 9M Years | 187M Years |
| 15 | 5 Hours | 890 Years | 47M Years | 613M Years | 14Bn Years |
| 16 | 2 Days | 23K Years | 2Bn Years | 26Bn Years | 1Tn Years |
| 17 | 3 Weeks | 812K Years | 539.72M Years | 2Tn Years | 95Tn Years |
| 18 | 10 Months | 22M Years | 7.23Bn Years | 96Tn Years | 6Qn Years |
Our Most Helpful Articles
Key Findings
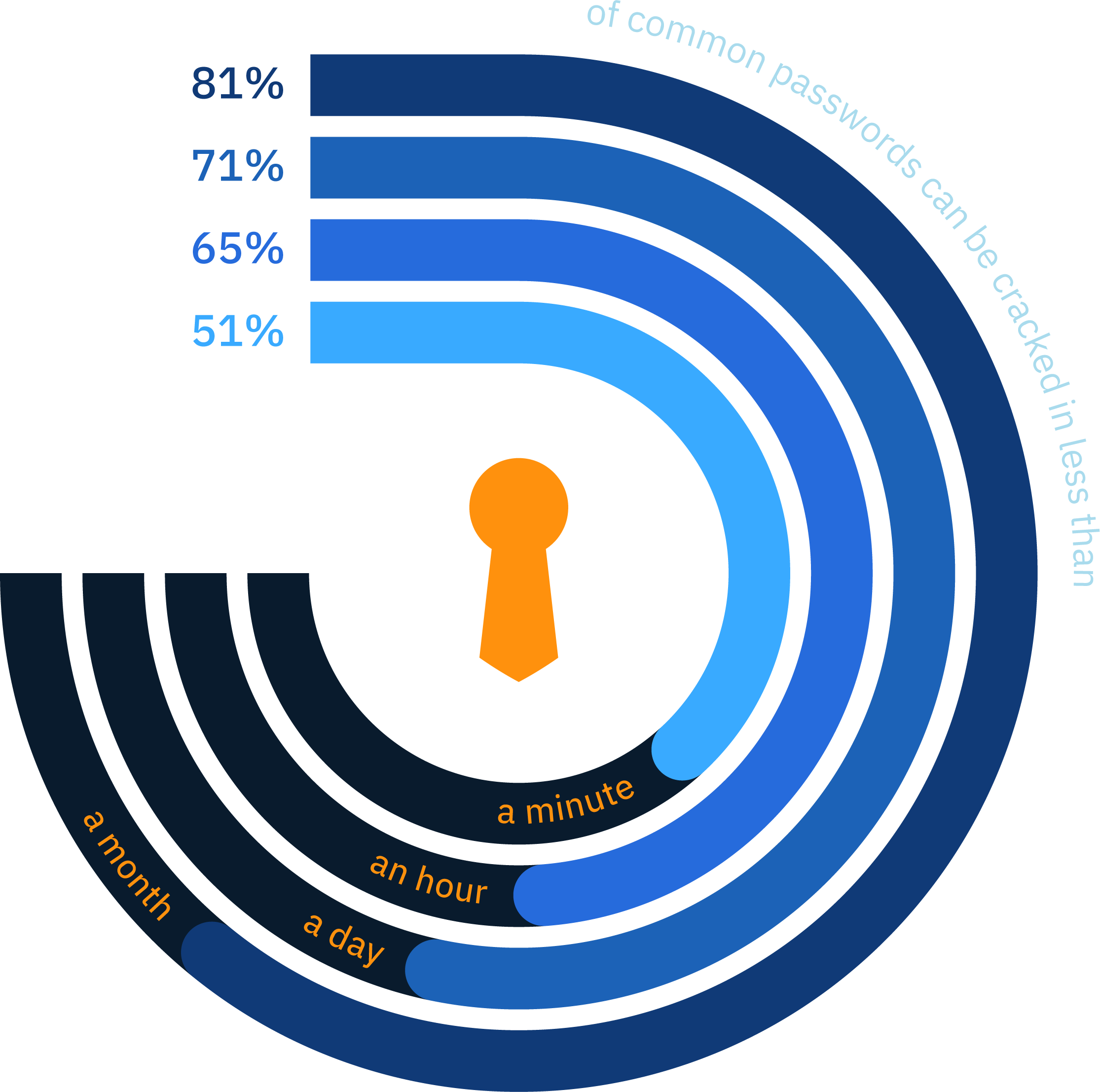
- 51% of common passwords
can be cracked in less than a min - 65% of common passwords
can be cracked in less than an hour - 71% of common passwords
can be cracked in less than a day - 81% of common passwords
can be cracked in less than a month
It takes PassGAN < 6 minutes
to crack any kind of
7 character password, even if it contains symbols
Passwords > 18 characters are generally safe agaisnt AI password crackers, as it takes PassGAN at least 10 months to crack number-only passwords and 6 quintillion years to crack passwords that contain symbols, numbers, lower-case letters, and upper-case letters.

10 months
6 Quintillion
years
18 characters
number-only
passwords
18 characters
contain symbols, numbers,
lower-case letters,
and upper-case letters.
What is PassGAN?
PassGAN represents a concerning advancement in password cracking techniques. This latest approach uses Generative Adversarial Network (GAN) to autonomously learn the distribution of real passwords from actual password leaks, eliminating the need for manual password analysis. While this makes password cracking faster and more efficient, it is a serious threat to your online security.
PassGAN can generate multiple password properties and improve the quality of predicted passwords, making it easier for cybercriminals to crack your passwords and gain access to your personal data. As such, it is crucial to regularly update your passwords to protect yourself from this dangerous technology.
How Does PassGAN Work?
To understand how PassGAN works, examining the framework behind many modern password guessing tools is important. Typically, password guessing tools operate using simple data-driven techniques. This means they apply data models that run manual password analyses. In addition, the tools make further assumptions about password patterns and use password generation rules like concatenation.
Guessing passwords using such strategies is relatively efficient for small-scale and predictable passwords. However, when the sample size is large and complex password patterns are involved, these tools become either too slow or completely incapable of cracking the security codes. This is where systems lik PassGAN come into play.
PassGAN is a shortened version of the words "Password" and "Generative Adversarial Networks" (GAN). GAN is the general mechanism that runs this password-hacking tool. At its core, the mechanism runs on a neural network.
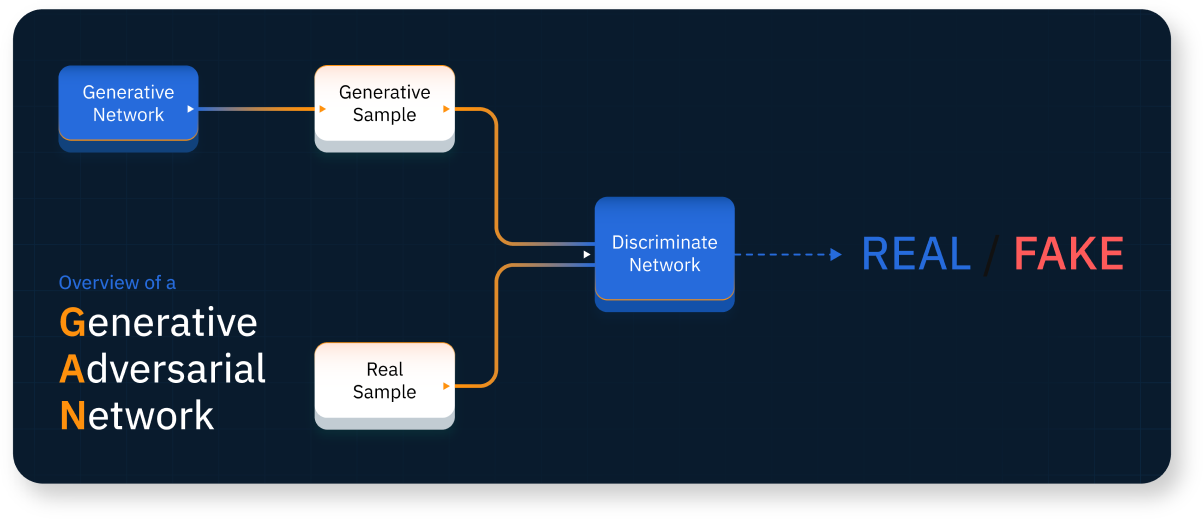
Neural networks are systems that train machines to interpret and analyze data like the human mind. GAN's neural networks are designed to record a variety of properties and structures. The technology was trained using the RockYou dataset, a data group used to train intelligent systems on password analysis. After training, GAN was able to leverage the acquired knowledge to create new sample passwords that follow the neural network distribution.
How Can You Protect Your Passwords?
It is very important to maintain the integrity of your passwords. Unfortunately, many password database leaks have revealed that people tend to use simpler, easier-to-hack passwords than more secure ones. How can you ensure your password is strong enough to resist a hack and keep you safe? Let's explore some of the best password protection solutions available.

01
Password strength is the main difference between an easy-to-hack password and a secure one. From the data obtained when we ran password samples on PassGAN, a digit-only password with ten characters can be instantly hacked.
A ten-letter password with only lowercase letters would take an hour to hack, while a ten-letter mixed-case password would take four weeks. On the other hand, a ten-character strong password using letters, symbols, and numbers would take five years to decipher.
This means the stronger your password, the lower the likelihood that people or AI systems can figure it out. Here's a list of factors that ensure your password strength is difficult to compromise.
- Use at least 15 characters.
- Have at least two letters (upper and lower-case), numbers, and symbols in the password.
- Avoid obvious password patterns, even if they have all the required character lengths and types.
02
A key way to maintain the security of your account is to change your password every 3 to 6 months. If you suspect that someone has accessed your account or that you have shared your password with someone who shouldn't have it, you should change your password immediately to prevent any security breaches.
03
Using the same password across all your accounts can be very risky. When someone breaches the password, they can easily access multiple accounts.
The best way to deal with this is to ensure you generate new passwords for every account.
The main password format can be consistent, but you can make slight adjustments based on the account in question. For instance, you can have 5711@FB_FaceBookIsLocked as your Facebook password and 1286_IG@IGIsLocked as your Instagram password.
Methodology
We took a list of 15,680,000 common passwords from the Rockyou dataset and used it for training and testing. We exclude all passwords that are longer than 18 characters or shorter than 4 characters from the scope of this experiment. The final list is then divided into subcategories with varying lengths and character types.
Finally, we used PassGAN to run through the list and record the results in terms of accuracy percentage and estimated prediction time.
Fair Use Statement
Please feel free to share our findings with anyone you know who might benefit from them. Our only request is that you include a link back to this page so that readers can access all relevant information and our contributors can be properly credited.